A Deep Dive into Lightning Network (LN) Security
This article is by guest author Jeremy Moser. The views and information presented here are those of the author.
Bitcoin and blockchain have undoubtedly revolutionized finance. The noble idea of decentralized finance has been becoming more popular in the past decade, and we can expect more projects and new implementations in the future.
However, Bitcoin is not without flaws. Early adopters faced many problems, some of which still exist. What’s essential is that solutions for those problems continuously emerge.
One of Bitcoin’s most significant improvements is the Lightning Network (LN). It helped solve major problems such as scalability and privacy. Furthermore, LN has made some crucial advancements in terms of security, which we will cover today.
What is the Lightning Network?
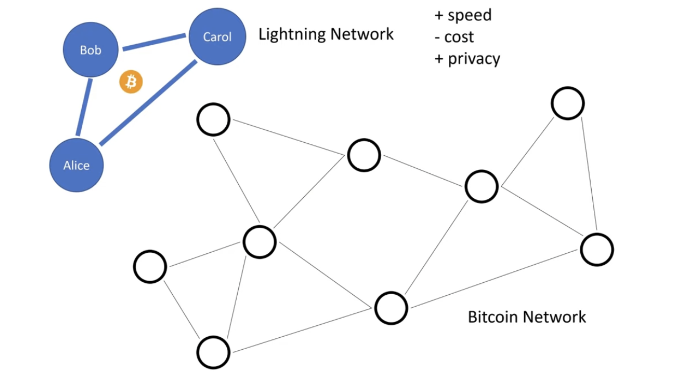
The Lightning Network solves one of Bitcoin’s most significant problems: scalability. This layer two solution leverages cryptography and smart contracts to help users make cheap transitions on the blockchain.
However, even though the idea was born with Bitcoin in mind, it’s also been applied to other blockchains, most notably Ethereum. Lightning Network was proposed in 2015, and it has been gaining popularity ever since.
The problem with Bitcoin is that transaction fees are calculated based on the traffic in the network rather than the value of the transaction. So whether you transfer $20 worth of Bitcoin or $1 million worth of it, you will pay the same amount.
While negligible for the second example, this prevents Bitcoin from being adopted for everyday expenses and costs. To fix this problem, Lightning Network has established payment channels that allow fast, low-cost transactions off-chain.
Once the private channel is created, parties can deposit Bitcoin into a multi-signature wallet, allowing safe and transparent transactions. Once the channel is established, parties can conduct an unlimited amount of transactions without worrying about fees or delays.
The transactions that happen in the lightning channels aren’t broadcast to the entire network, and only individuals can gain insight. Once the transactions are done, the final state of the channel balance is recorded.
So, whether two or millions of transactions occurred between the parties, they will be recorded as a single one on the blockchain.
Advantages That Lightning Network Brings
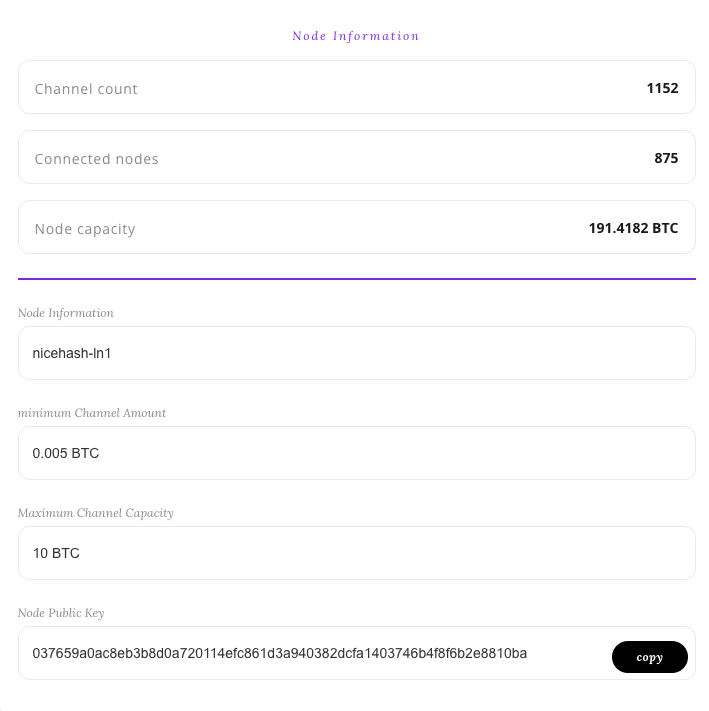
As mentioned earlier, the Lightning Network helps a lot with micropayments. The default lowest amount of Bitcoin that you can transfer is 0.0000054 BTC, but LN lowers this number to 0.00000001 BTC or one Satoshi.
Again, let’s go back to the idea of using Bitcoin for everyday payments. If a fast food restaurant allows Bitcoin payments, you would want to make them quickly and without additional fees. Because of network congestion, transaction times can be longer, and it would be pointless to wait until the transaction happens before you can go ahead and proceed with your meal.
The Lightning Network could be revolutionary in bringing Bitcoin closer to everyday uses. However, LN also allows Bitcoin to become widespread in terms of scalability. With LN, you can make millions of transactions without clogging the network.
This means that it also allows Bitcoin to become more popular and adopted on a global scale. For example, transactions between whales or between individuals and exchanges will be more affordable to everyone involved.
Although Bitcoin is designed to increase privacy and anonymity, lacking in traditional finance, Bitcoin’s Lightning Network further increases the confidentiality of the parties involved in transactions by hiding the amount transferred before the channel is closed.
It’s incredible how these advantages tackle entirely, or at least partially, some of the most notable downsides of Bitcoin. Besides Bitcoin, LN has necessary implementations, which include:
- Lightning Network Daemon (LND)
- C-lightning
- Eclair
How Does Lightning Network Achieve Security?
If you’ve spent some time researching a bit more obscure part of the internet, then you’ve likely heard about Tor. What’s essential about Tor is the idea of onion routing, which increases the privacy and anonymity of internet users.
Onion routing encrypts messages between different nodes, which is especially helpful in payment channels. This is also similar to peer-to-peer principles, as nodes can only see the steps in front of them and those before them. Furthermore, LN implements private channels, which further protect the involved parties.
Another security problem that’s also notable in traditional computer networks is Denial-of-Service attacks. This type of malicious activity focuses on bombarding the network with traffic, preventing the server from being accessible.
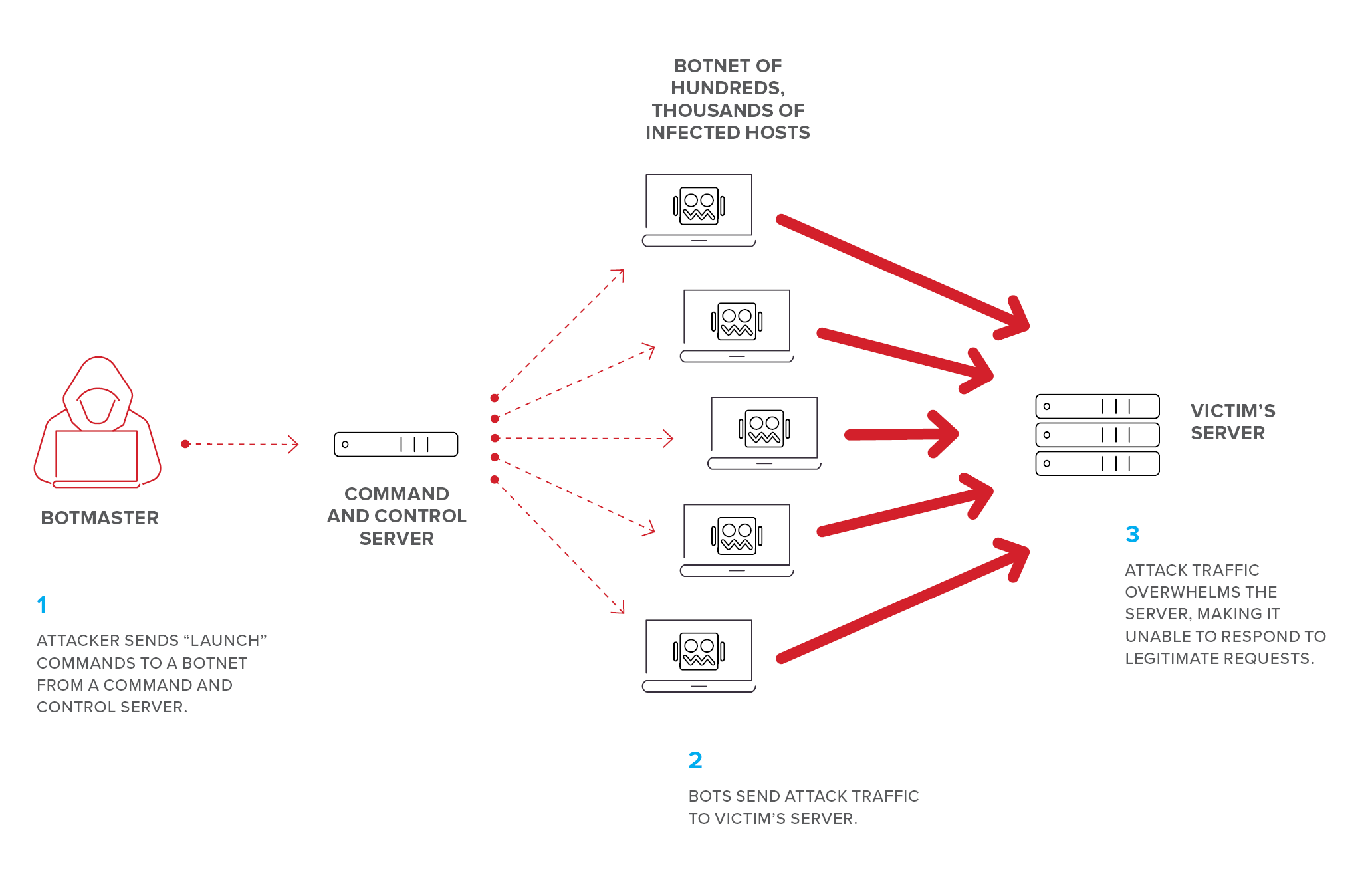
An enhanced version of this attack is a Dedicated DoS attack, which uses multiple devices to target a specific network. Traditional computer networks solve this problem by being scalable, thus preventing the traffic from overwhelming the servers. Other solutions include forbidding devices from particular regions or IP addresses from being able to access the server.
The Lightning Network’s approach to solving this problem is different but amusing. LN charges higher fees for transactions that are processed first, making DoS attacks either too expensive or impossible to execute. Additionally, implementing multi-factor authentication (MFA) can further bolster protection by requiring more than just a password for access."
The last type of attack that cryptocurrencies face yet the Lightning Network has solved is “channel breach.” This problem occurs when a malicious third party tries to intercept the communication between two parties in the channel, allowing the individual to access the funds.
Lightning Network solves this by outsourcing channel protection and monitoring to “watchtower” services, which secure the channel without being necessary for them to see the ongoing traffic between the parties.
Additional Security Enhancements
Blockchain technology is developed with privacy and security in mind. However, you shouldn’t rely only on the built-in mechanisms. Companies that create crypto products and services have other processes and departments that can become targets of malicious activities.
It is important to be vigilant about security as a whole. Developers working on crypto projects leverage tools such as endpoint monitoring software to improve security in the system as a whole.
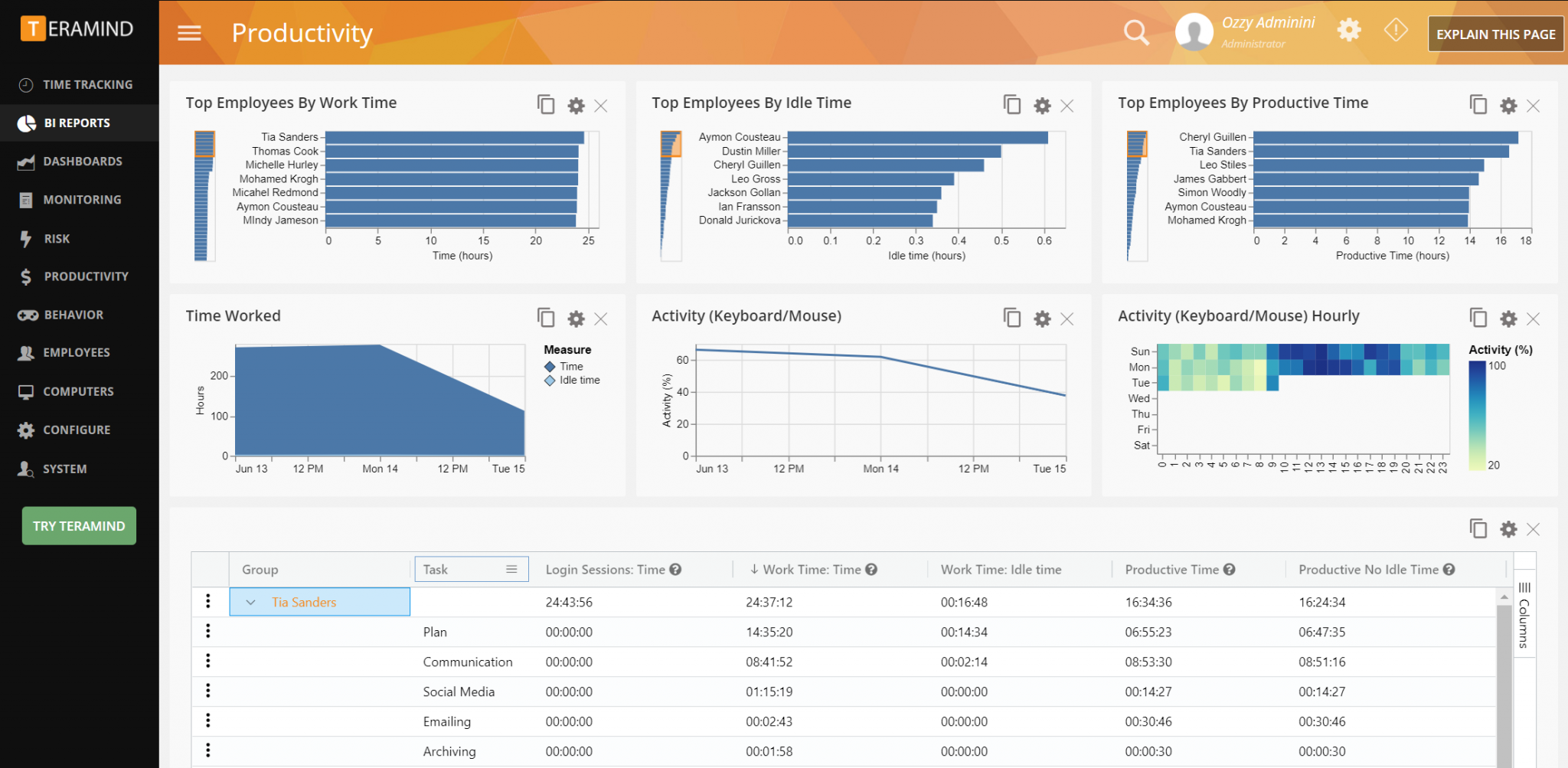
Overall, it’s not only a single node that’s secure or not; it’s the system. Just like how computers are as fast as their slowest component, networks are just as safe as the weakest link. Endpoint monitoring is only one of the things you can leverage to improve your company’s security.
However, crypto projects can vary from DeFi platforms and play-to-earn projects to vast crypto institutions with global reach. When an individual’s financial state is questioned, there shouldn’t be ambiguities.
One way to help your customers and/or users is to implement customer support and publish an extensive knowledge base. Furthermore, many crypto projects organize AMAs on YouTube and Telegram to answer specific questions.
If you opt to implement customer support, you can leverage customer experience insights to address user concerns about your project. This software can help:
- Ensure that users receive consistent and accurate information
- Track and document past security issues
- Manage high volumes of questions
Future Evolution of the Crypto Landscape
The cryptocurrency landscape is continuously evolving, and every few years, we see noticeable improvements that improve the lives of cryptocurrency holders and businesses. The Lightning Network is only one of the many solutions that have emerged.
If you’re developing your crypto project, consider the Lightning Network as a stepping stone for future improvements and consider what problems persist. For example, Linux kernel developers have leveraged eBPF technology to improve system observability and security.
Similarly, blockchain developers can use innovative solutions such as Lightning Networks to drive the Bitcoin market forward and solve significant problems that still exist in the industry.
Lightning Network Solves Important Shortcomings of Blockchain
Traditional finance has existed for centuries, and there are still various problems. It would be unfair to expect Bitcoin to be perfect since it’s only been around for about a decade. However, observing the various emerging advancements is incredible, with Lightning Network being one of the most notable ones.
If you are a crypto developer, this article should hopefully help you feel more comfortable implementing the Lightning Network for your project. Furthermore, if your primary concern about implementing innovative solutions was security, you have the right mindset.
There’s no such thing as worrying too much about security. With problems such as DoS Attacks, channel breaches, and routing attacks out of the way, you can focus on developing or improving other features of your crypto project.