The Role of Payment Splitting and Switching in Improving Privacy in Lightning Transactions
Since Bitcoin broke the $40,000 resistance on December 3rd, the pioneering cryptocurrency regained the April 2022 level. That period was sandwiched between the start of the Fed’s interest rate hiking cycle and Terra (LUNA) crash.
While it is yet uncertain where Bitcoin’s latest bullrun will head, there is little ambiguity about something else - Bitcoin fees. For the bulk of the year, the average BTC transaction fee has been firmly under $5. The renewed Bitcoin interest, riding the ETF approvals hype, has now elevated it to just under $30 per transaction.
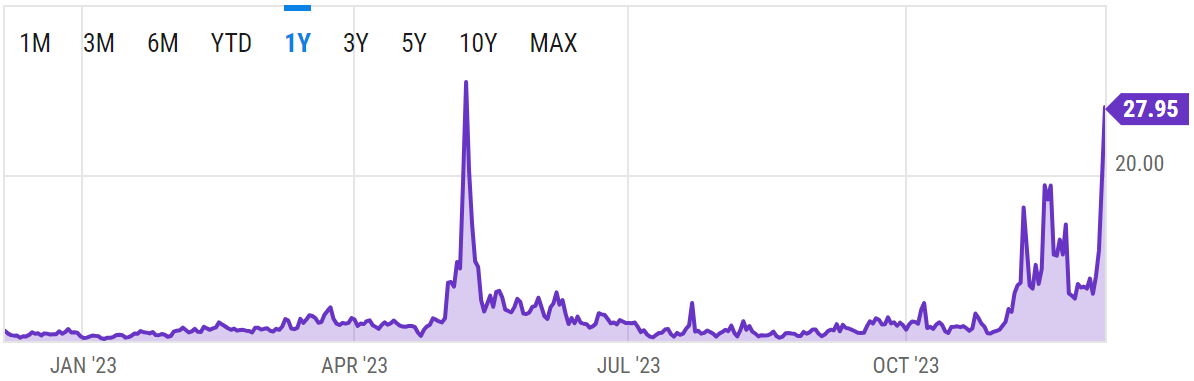 The more popular Bitcoin gets, the costlier BTC transfers are. Image credit: ycharts
The more popular Bitcoin gets, the costlier BTC transfers are. Image credit: ycharts
This is not surprising. In the aftermath of the Blocksize War debate from 2015 to 2017, Bitcoin blockchain settled to process infrequent but high-value transactions. In turn, the “digital gold” narrative was affirmed.
Nonetheless, if the Bitcoin network is limited to 7 transactions per second, thus incurring high fees during high traffic, how can it ever receive global mass adoption? What about frequent micro-tipping, online shopping, incurring subscriptions, in-game purchases, or even in future trading strategies?
These daily habits require low friction, with the tiniest sums of money lost. So tiny that one could discard them. Bitcoin’s layer 2 scaling solution, Lightning Network, made great inroads to address this friction problem. But there are still some challenges to solve.
Unlocking Bitcoin’s Potential with Lightning Network
As a network of off-chain payment channels, Lightning Network bypasses Bitcoin mainnet’s bottleneck. The concept is quite simple. Two transacting parties open a channel between them, which is established when BTC funds are deposited to an off-chain ledger.
Because the off-chain ledger, as a layer 2 network, doesn’t record transactions on Bitcoin’s network, no Bitcoin miners incur fees. Instead, as many transactions can occur with negligible friction, near-instantly.
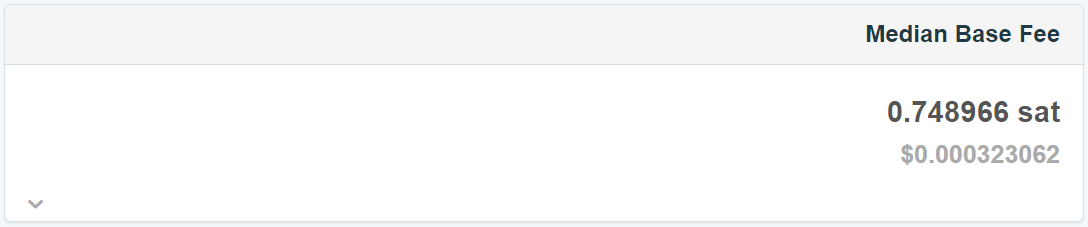 The LN fee is orders of magnitude lower. Image credit: 1ml.com statistics.
The LN fee is orders of magnitude lower. Image credit: 1ml.com statistics.
Only after the payment channel is closed, manually or automatically, are those transactions rolled up into a single transaction. Then, that consolidated LN transaction is broadcasted to Bitcoin mainnet for final confirmation, subject to miner fees. But what happens if party B doesn’t acknowledge the receipt from party A?
Lightning Network solved this issue of trust with an integrated refund option. Following the payment channel funding, refund can be activated (unlocked) after a certain period. Both parties sign the refund terms, so it can be exercised unilaterally.
Unfortunately, despite speed and low friction, LN payments suffer a drawback due to how BTC payments are moved through channels.
Understanding Lightning Network's Current Privacy Challenges
Another way to frame LN scaling is to describe it as collateral forwarding. In that architecture, LN nodes serve as intermediaries, earning node-hosting fees in the routing process. In turn, nodes with a solid uptime record and efficient routing can earn higher fees.
Presently, LN nodes facilitate ~8.3 payment channels on average, with the average node age of two years. As one might guess, the friction happens in the routing process. Users are incentivized to indirectly link between channels. After all, opening and closing channels exerts a blockchain fee.
To that end, payments can be routed via multiple channels hosted by third parties. Those routing fees too are orders of magnitude lower than simply using Bitcoin mainnet. But during that gossip process that probes for routing, user information leaks.
In other words, the very act of forwarding payments most cost-effectively necessitates information gathering. That information gathering, to determine the accurate state of LN channels, is called channel probing. It not only improves payment friction but reduces fraud risk.
During channel probing, the sender data has a cloak of privacy owing to onion encryption routing. Yet, the same is not so true for payment receivers.
During channel probing, the sender data has a cloak of privacy owing to onion encryption routing. Yet, the same is not so true for payment receivers.
— Tony Giorgio, Lightning Network developer
One of those areas of improvement is to route payments through multiple intermediaries to obfuscate the routing, making it more difficult to source-track the payment. Users could also make incoming payments “blind” via encryption. As the payment is forwarded, route blinding ensures that only the receiver views its entire path.
LN’s Payment Splitting and Switching Mechanisms
As Lightning Labs works to implement privacy enhancement at the core protocol level, a related technique to route blinding is payment splitting and switching (PSS). While route blinding obscures some sections of the payment path, PSS splits it into smaller portions.
These smaller payment bits are then forwarded over alternative routes to both enhance privacy and increase the likelihood of the payment’s success. Developer of the PSS technique, Gijs van Dam, explained it in the following steps:
- Alice and Bob (the intermediary) open a payment channel that supports PSS.
- Alice splits the payment she wants to send into two parts.
- One part follows the original route to Bob, while the other part goes through an alternative route.
- Alice will commit the original route forwarding through HTLC - hashed-timelock-contract - with a lower BTC amount than required by Bob.
- Upon seeing the inefficient sum, Bob waits for an agreed upon figure, the second installment, because he supports PSS.
- Alice then sends a new payment to fill up the inefficient sum, using the same transaction hash.
Of course, when Bob receives the payment that also covers the forwarding fee, he is then incentivized to forward the original payment. He would do so through HTCL as well. It bears keeping in mind that HTLC is LN’s underlying building block. These smart contracts facilitate:
- Fund locking
- Fund unlocking
- Off-chain routing
- Timelock mechanism
- Preimage commitment
Preimage commitment is a cryptographic puzzle with a unique solution only Alice knows. In other words, Bob can only claim payments with a revealed preimage that generates the payment hash.
Altogether, PSS makes it possible for LN nodes to forward payments using any route available via “localized packet switching”. The question is, how does PSS boost the Lightning Network privacy?
Enhancing Privacy with Payment Splitting and Switching
Let’s go back to channel probing, as the necessary requirement of the LN architecture. If that channel is now PSS-supported, how would potential attackers be thwarted?
With PSS packet switching, the attacker would have to take into account that payment could go through any possible Alice-Bob route simultaneously. With that in mind, the attacker would have to probe total liquidity between Alice and Bob.
Biryukov et al. (2022) developed the LN Probing Simulator to test such likelihood. It can be conducted in two ways:
Direct probing - attacker opens a channel to one of the two nodes (on either side) of the targeted channel. Not only would Alice/Bob have to participate when opening the channel, but the attacker would suffer on-chain fees for each probed channel.
In this case, the payment would be routed through exactly two nodes. As 2-hop payment it would be less expensive, typically used for smaller sums.
Remote probing - the attacker foregoes direct channel link. Instead, they choose which node to connect in order to avoid on-chain fees.
Because remote probing is run through a multi-hop, the attacker could gather data on intermediaries like Bob. However, this probing is likely to fail if the intermediary lacks funds to relay the payment.
In graph form, this means that for both direct and remote probing the information gain is reduced if PSS is enabled.
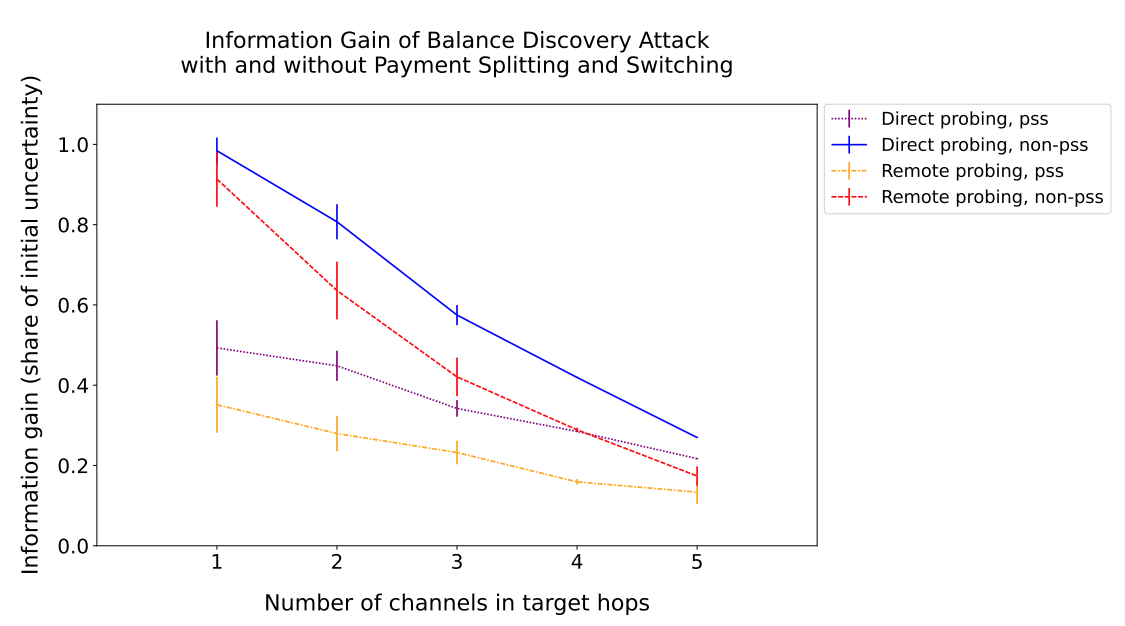 Image credit: Gijs van Dam∗
Image credit: Gijs van Dam∗
Moreover, because the potential attacker lacks the knowledge if PSS is enabled or not, this creates another layer of uncertainty. The attacker would only be able to tell this if linking to both node peers on either side of the channel, which would bring about the aforementioned on-chain fee problem.
Overall, simulations conducted by Gijs van Dam show that PSS could drop information gain by 50% for direct probing and 62% for remote probing. On top of this, the new PSS technique leads to such complexity that Balance Disclosure Attacks (BDA) would require off-the-shelf hardware to properly scale up.
Conclusion
For regular banking users, it is difficult to appreciate what it means to have an open-source, permissionless storage and payment system. In such a traditional system, parties don’t seek sovereignty. Instead, they form a contract of permissioned custody.
Bitcoin broke that paradigm with true private, permissionless wealth storage and transfer. Yet, to ensure that such a network remains decentralized, a compromise had to happen in the form of smaller block sizes. And if block sizes for transactions are small, the network’s throughput is lower, eventually incurring higher transfer fees.
Lightning Network came in as a scaling solution to solve this, upgrading Bitcoin from store-of-value to low friction currency. Still, some laws are difficult to circumvent. Transaction data still has to be publicly broadcasted through LN channels for payments to happen.
During this broadcasting, user info can be deanonymized. Among many techniques to safeguard privacy, Payment Splitting and Switching (PSS) comes to the rescue. Would-be attackers then have to deal with greater costs and complexity to break through it and succeed in Balance Disclosure Attacks (BDA).
Although not perfect, PSS shows that LN has ample room for improvement. More importantly, it shows that Lightning Network itself can continue to scale the Bitcoin network while retaining its conservative nature.