What is a Zero-Knowledge (ZK) Proof?
Lately, a new buzzword has been noticed in the crypto mining industry - Zero-Knowledge Proof or ZK coins.
What is zero-knowledge proof, and why are there so many people talking about it? As with everything else, one must understand the problem before understanding the solution.
What problem does a zero-knowledge proof solve?
Zero-knowledge proofs solve several problems related to privacy and security in various domains. Here are a few examples:
- Authentication and Identity Verification: Zero-knowledge proofs can be used to prove identity without revealing any personal information. For example, a user can prove that they are over 18 years old, without revealing their exact date of birth.
- Data Privacy: Zero-knowledge proofs can be used to validate sensitive data, such as medical records or financial transactions, without revealing the actual data. This allows for secure data sharing and analysis while preserving privacy.
- Blockchain Technology: Some blockchain technologies use zero-knowledge proofs to verify transactions without revealing the details. This helps to ensure the confidentiality and privacy of transactions on the blockchain.
- Cybersecurity: Zero-knowledge proofs can be used to authenticate users without revealing their passwords or other sensitive information. This helps to prevent identity theft and other forms of cybercrime.
What are zero-knowledge proofs?
Zero-knowledge proofs are a cryptographic protocol that enables one party, the prover, to prove to another party, the verifier, that a statement is true without revealing any additional information beyond the truth of the statement itself. In other words, the prover can convince the verifier that they know something without actually revealing what they know. This is achieved by using complex cryptographic algorithms to create proof that can be verified without revealing any information about the proof itself. Zero-knowledge proofs are useful in scenarios where privacy is crucial, such as in online transactions, identity verification, and other applications where sensitive information needs to be protected.
The zero-knowledge proofs have three requirements:
- Completeness: Both the prover and verifier are expected to abide by the protocol honestly.
- Soundness: Assuming the prover is not honest and lacks knowledge of a secret, they are unlikely to persuade the verifier that they possess the secret, as the probability of deceiving the verifier is too low.
- Zero-Knowledge: This refers to a scenario where a prover (Bob) is set to demonstrate to a verifier (Alice) that they have knowledge of a secret. However, the demonstration only convinces (Alice) of the secret knowledge possessed by (Bob) with no means for outsiders to ascertain the veracity of proof.
Ali Baba Cave Experiment
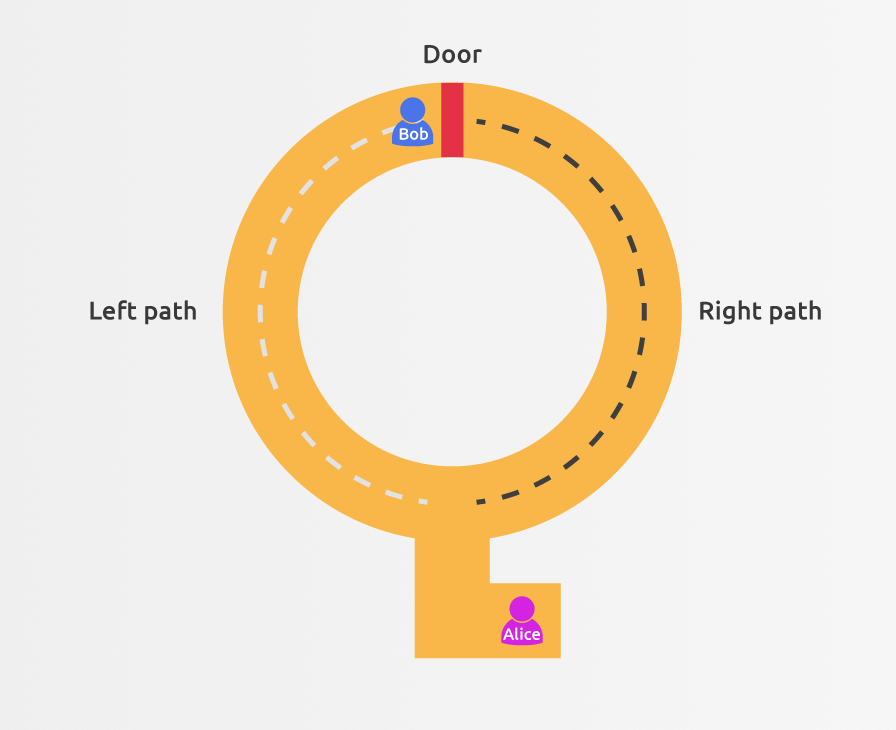
The Ali Baba cave example is a commonly used illustration of zero-knowledge proofs. In this scenario, Bob and Alice enter a cave with doors on the opposite side of the entrance, they both know the code to open them. Bob claims to know the code and wants to prove it to Alice without revealing it.
To do so, Bob enters the cave on the left side and walks to the doors on the opposite side. Meanwhile, Alice waits at the entrance and asks Bob to come out on the right side of the cave. If Bob successfully opens the door and emerges from the right side, he must know the code. However, Alice does not know if Bob used the right or left path at the beginning.
This test is repeated multiple times, with Alice asking Bob to emerge from different sides of the cave. If Bob consistently emerges from the correct side of the cave, Alice can be confident that he knows the secret code without actually learning the code itself.
In this way, the Alibaba cave example demonstrates how zero-knowledge proofs can be used to verify a claim without revealing any sensitive information.
What practical problem can a zero-knowledge proof solve?
A good practical example of a problem is smart contract publicity. Smart contracts are written on the public blockchain and can be observed by anyone. A smart contract can, for example, have a written condition that will release the locked funds to a user after this condition has been met. Currently, this condition can be observed by anyone via blockchain explorers.
With zero-knowledge proof, one party could prove that the condition has been met without revealing any other information about the smart contract or conditions inside that smart contract.
Another use case could be proving proof of reserves of crypto exchanges. Maybe the exchange does not feel comfortable sharing public information about the public keys of wallets that they use for cold storage. But they can use zero-knowledge proof to confirm that they have the reserves without revealing any other information. The “verifier” of this statement can be sure that the exchange indeed holds reserves.